24 Mart’ta Yıldız Teknik Üniversitesi Adli Bilimler Günü kapsaminda “Otomotiv Siber Güvenlik ve Adli Bilişim” sunumunu gerceklestirdik. Yıldız Teknik Üniversitesi Biyoteknoloji ve Genetik Kulubune tesekkur ederiz





Ankara Üniversitesi Sürekli Eğitim Merkezi (ANKÜSEM) ile Sirius Kriminal Danışmanlık ve Eğitim Hizmetleri Limited Şirketi "Eğitim İşbirliği Protokolü" imzaladı.
Bu iş birliği, akademik bilgi ile saha deneyimini bir araya getiren çok değerli bir adım olduğunu değerlendiriyoruz.
Ankara Üniversitesi Sürekli Eğitim Merkezi (ANKÜSEM) ile Sirius Kriminal Danışmanlık ve Eğitim Hizmetleri Limited Şirketi arasında imzalanan protokolün; kriminal inceleme ve adli analiz alanlarında uygulama temelli, nitelikli eğitim programlarının geliştirilmesine önemli katkı sağlayacağına inanıyoruz.
Üniversite–sektör iş birliğini güçlendirecek bu çalışmanın hayırlı ve başarılı olmasını dileriz.



Deepfake’ler: Görünen Tehditten Daha Fazlası
Deepfake’ler ve sentetik medya artık yalnızca bir teknoloji meselesi değil;
🔹 bireylerin itibarı,
🔹 kurumların güvenilirliği,
🔹 demokratik süreçler ve
🔹 toplumsal güven
üzerinde doğrudan etkisi olan çok boyutlu bir risk alanı.
Asıl tehlike yalnızca sahte içeriklerin üretilmesi değil, gerçek içeriklerin de “deepfake olabilir” şüphesiyle değersizleştirilmesi. Bu durum literatürde “The Liar’s Dividend” olarak tanımlanıyor: Gerçekler inkâr edilebilir hâle geliyor, hesap verebilirlik zayıflıyor, güven erozyona uğruyor.
Bu nedenle çözüm yalnızca teknik tespit araçlarında değil;
✔️ eğitimde,
✔️ hukuki çerçevede,
✔️ kurumsal hazırlıkta
ve en önemlisi çok paydaşlı iş birliğinde yatıyor.
Deepfake’lere karşı mücadele, koordineli ve kolektif bir yaklaşım gerektiriyor.
Kamu, özel sektör, akademi ve sivil toplum birlikte hareket etmeden bu tehdit yönetilemez.
Güven, korunması gereken bir altyapıdır.
Deepfakes: A Threat Beyond Technology
Deepfakes and synthetic media are no longer just a technical challenge.
They directly affect:
🔹 individual reputations,
🔹 institutional credibility,
🔹 democratic processes, and
🔹 societal trust.
The real danger is not only fabricated content — but the erosion of trust in authentic content. This phenomenon, known as “The Liar’s Dividend,” allows bad actors to dismiss real events as fake, avoid accountability, and undermine trusted institutions.
Mitigation cannot rely on detection technologies alone.
It requires:
✔️ education and media literacy,
✔️ legal and regulatory frameworks,
✔️ organizational preparedness, and
✔️ most importantly, cross-sector collaboration.
Addressing deepfakes demands a coordinated, multi-stakeholder response across government, industry, academia, and civil society.
Trust is critical infrastructure — and it must be protected.
Kaynak: Homeland Source: Homeland
Derleyen: Mehmet ŞEN, Emniyet Müdürü (E)
Compiled by Mehmet SEN, Retired Chief Superintendent
Araç–yaya çarpışmalarında yayanın hareketi; çarpma hızının belirlenmesi, kazanın yeniden yapılandırılması ve adli değerlendirme açısından kritik öneme sahiptir.
Bu çalışmada;
-Yayanın araç üzerinden takla (vault) hareketi,
-Uçuş ve kayma mesafelerine dayalı hız tahmin yöntemleri,
-Vault denklemi, kayma denklemi ve Limpert (1990) ampirik modeli,
-Reaksiyon süresi ve durma mesafesi esaslı analizler
adli mühendislik perspektifiyle ele alınmıştır.
📌 Özellikle 48 km/s üzerindeki hızlarda baş yaralanmalarının ölümcül sonuçlara yol açabildiği, matematiksel ve sahaya dayalı verilerle ortaya konmaktadır.
Adli trafik incelemelerinde bilimsel yöntemlerin önemi bir kez daha görülmektedir.
✍️ Derleyen: Mehmet ŞEN
Emekli Emniyet Müdürü – Sirius Kriminal Kurucu Ortak
Kaynak: Kazanın yeniden yapılandırılmasında matematik metotları, Adli mühendislik perspektifi, Harold Franck, Darrel Franck
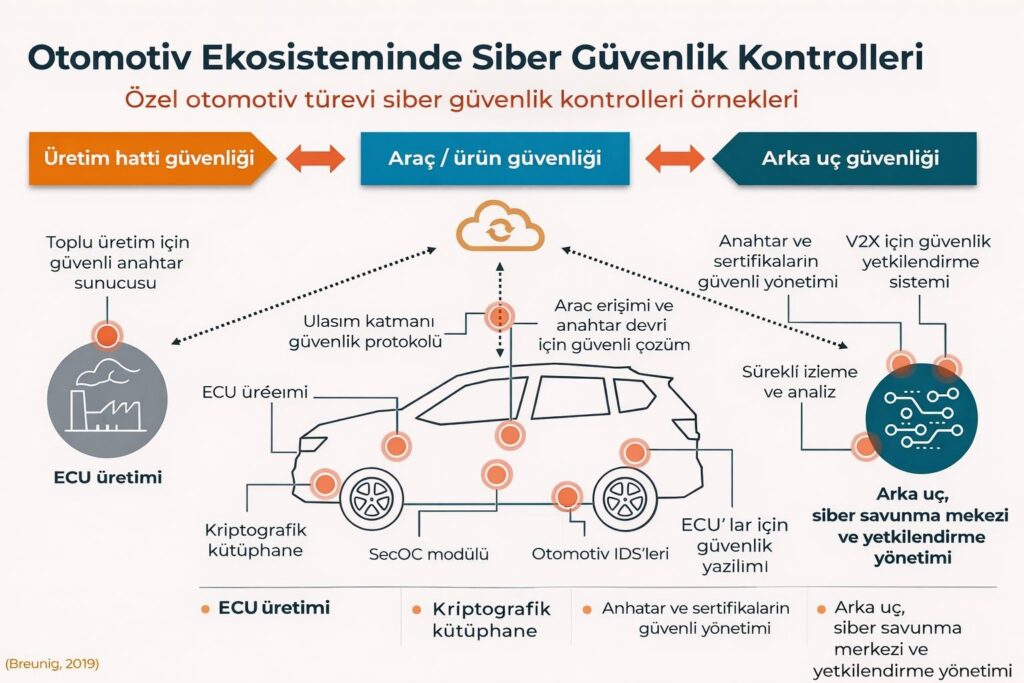
Dijitalleşen otomotiv dünyasında siber güvenlik artık yalnızca araç içi yazılımlarla sınırlı değil. Üretim hattından araca, backend altyapısından V2X iletişimine kadar tüm ekosistemi kapsayan bütüncül bir güvenlik mimarisi gerektiriyor.
-Üretim hattı güvenliği
-Araç / ürün içi siber güvenlik kontrolleri
-Arka uç (backend) kimlik, anahtar ve izleme sistemleri
birbirine bağlı bir zincir olarak değerlendirilmesi gerekiyor
ISO/SAE 21434, UNECE R155–R156 ve modern OT/IT entegrasyonu perspektifinde; siber güvenlik artık bir “opsiyon” değil, fonksiyonel güvenliğin ayrılmaz bir parçası.
Güvenli üretilmeyen bir araç, sahada güvenli olamaz.
Kaynak: Breuing, 2019
In forensic evaluations of road traffic accidents, accurate interpretation of injuries is crucial for reconstructing the event.
The direction of abrasions can provide valuable information about the victim’s movement after impact. At the same time, it must be remembered that extremities (arms and legs) are mobile structures.
Therefore, injuries on the trunk and extremities should be assessed together, considering different limb positions.
This holistic approach improves:
accident reconstruction,
pedestrian–vehicle impact analysis,
expert witness reporting and forensic consistency.
makes it more scientifically sound, consistent, and defensible
In forensic medicine, details are not just details — they are the path to the truth.
Sirius Kriminal has signed a Memorandum of Understanding with the
Limited Liability Partnership “Alliance of Independent Forensic Expertise in Kazakhistan

Is Your Vehicle a Threat to National Security? It Could Be — Regardless of Where It Was Manufactured.
Yayınlanma tarihi: 2 Ekim 2024, 05:03 (CEST)
Nisan ayında, ABD’li milletvekilleri Başkan Joe Biden’a Çin yapımı elektrikli araçları (EV) yasaklaması çağrısında bulundu. Bu araçları, “Amerikan otomotiv endüstrisine varoluşsal bir tehdit” olarak nitelendirdi.
Yasak önerisi, Çinli otomobil üreticilerinin devlet desteği sayesinde haksız bir avantaja sahip oldukları yönündeki endişelerden doğdu.
Aylar süren dijital bağlantılarla ilgili bir soruşturmanın ardından – bu bağlantıların Çin’in casusluk veya sabotaj faaliyetlerine olanak tanıyabileceği değerlendirildi –
Biden yönetimi geçtiğimiz haftalarda Çin yapımı araçların yasaklanmasına yönelik yeni kurallar önerdi.
Bu tehditlerin temelinde, bu araçların yazılım güncellemeleri ve çeşitli uzaktan kontroller için kullanılan yerleşik internet bağlantıları bulunuyor.
Yazar:
Dennis B. Desmond
Siber İstihbarat ve Siber Suç Araştırmaları Öğretim Görevlisi,
University of the Sunshine Coast
Açıklama:
Dennis B. Desmond, bu makaleden çıkar sağlayacak hiçbir şirket veya kuruluşla çalışmamaktadır. Tüm görüşler yalnızca akademik niteliktedir.
BD, Çin yapımı elektrikli araçları ulusal güvenlik gerekçesiyle yasaklamakta haklı mı? Peki Avustralya da aynı yolu mu izlemeli?
Nisan ayında, ABD’li milletvekilleri Başkan Joe Biden’a Çin yapımı elektrikli araçların (EV) yasaklanması çağrısında bulundu. Bu araçlar, “Amerikan otomotiv endüstrisi için varoluşsal bir tehdit” olarak nitelendirildi.
Yasak önerisi, Çinli otomobil üreticilerinin devlet desteği sayesinde haksız bir avantaja sahip oldukları yönündeki endişelerden kaynaklandı.
Aylar süren dijital bağlantılara ilişkin bir soruşturmanın ardından — bu bağlantıların Çin casusluğuna veya sabotajına imkân verebileceği tespit edildi — Biden yönetimi son haftalarda Çin yapımı araçların yasaklanmasına yönelik yeni düzenlemeler önerdi.
Yetkililerin belirttiği tehditler, araçlarda yer alan yazılım güncellemeleri ve uzaktan kontrol işlevleri için kullanılan dahili internet bağlantılarından kaynaklanıyor.
ABD’nin Çin yapımı araçları ulusal güvenlik gerekçesiyle yasaklama girişimi haklı mı?
Ve Avustralya da aynı yolu mu izlemeli?
Çinli araçlarda uzaktan erişim ve veri aktarımı temel bir bileşen; ancak aynı durum bugün pek çok ülkenin modern araçları için de geçerli.
Yine de Avustralya’nın Pekin ile ilişkileri zaman zaman gergin olduğundan,
ülkede satılan araçların hangi verileri Çin’e gönderdiğini ve bu araçların uzaktan erişim veya kontrol açısından ne kadar savunmasız olduğunu anlamak kritik önemdedir.
Kolaylık mı, çift taraflı bir kılıç mı?
Birçok otomobil üreticisi, araç fonksiyonlarının uzaktan kontrol edilmesini sağlayan hizmetler sunuyor. Bu özellikler kullanıcı açısından son derece pratik, ancak aynı zamanda kontrol, gizlilik ve güvenlik açısından ciddi soru işaretleri doğuruyor.
Günümüzün araçları artık tekerlekli bilgisayarlar gibidir. Araçlar ve sürücüler hakkında sürekli veri toplarlar; bu veriler hem uzaktan hem de servis sırasında erişilebilir.
Bu tür bilgisayarlı kontrol sistemleri ve izleme altyapıları (diğer adıyla telematik sistemler), otomotiv dünyasında giderek yaygın hale gelmiştir.
Konu elektrikli ya da benzinli araç olması değil — veriye kimin ve nasıl eriştiği. Araç ister elektrikli ister benzinli olsun, asıl endişe konusu tüm bu verilere kimin eriştiği ve nasıl eriştiğidir.
Eğer bu veriler internet üzerinden gönderilmiyor, sadece yerel serviste indirilip analiz ediliyorsa, bu durum görece olarak daha az endişe verici sayılabilir.
OnStar – Uzaktan bağlantının öncüsü
OnStar, 1996 yılında General Motors tarafından kurulan bir yan kuruluştur ve
araç telematik sistemleri ile uzaktan bağlantı teknolojilerinin öncüsü olmuştur.
ABD’deki hukuk uygulama kurumları ve istihbarat teşkilatları, geçmişte OnStar’ın hizmetlerini şu amaçlarla kullanmıştır:
- Araçların konumlarını izlemek,
- Araç içi konuşmaları dinlemek,
- Ve hatta kovalamaca sırasında araçların hızını düşürmek.
Artık araç üreticilerinin güncellemeleri, yeni özellikleri ve performans iyileştirmelerini uzaktan sunması olağan hale geldi.
Volkswagen’in bağlı hizmet uygulaması, uzaktan motor çalıştırma, kapı kilitleme, araç durumu kontrolü, yol yardımı, araç sağlık raporu ve servis planlama gibi özellikler içeriyor.
Benzer uygulamalar Ford, Mazda ve BMW gibi diğer markalar için de mevcut.
Bu yılın başlarında polis, Melbourne’da çalınan bir Ford Ranger aracını, üreticinin uygulamasındaki konum izleme özelliği sayesinde buldu.
Çinli markalar da benzer bağlantılı hizmetler sunuyor
Çinli otomobil üreticileri Haval ve GWM, Avustralya’daki elektrikli ve benzinli araçları için bağlantılı hizmetler sağlıyor. Bazı GWM modellerinde bulunan “T-Box” telematik donanımı, aracın internete bağlanmasına olanak tanıyor.
Üreticinin mobil uygulaması üzerinden etkinleştirildiğinde, GWM bağlantı servvisleri şu verileri topluyor:
- Sıcaklık,
- Akü durumu,
- Tahmini menzil,
- Kilometre,
- Lastik basıncı,
- Ve araç konumu.
Ayrıca sistem, kapı kilitleri, farlar ve diğer bazı işlevleri uzaktan kontrol edebiliyor.
Bağlantılı araçlarda gizlilik endişeleri yeni değil – ancak artık mesele daha derin
İnternete bağlı araçlarla ilgili gizlilik endişeleri uzun süredir dile getiriliyor.
Ancak son dönemdeki tartışmalar, bunun ulusal güvenlik boyutuna taşındığını gösteriyor.
Araçların bu kadar yoğun bağlantılı hale gelmesi, siber saldırganların veya hatta devlet aktörlerinin bu sistemleri hedef alabilmesine olanak tanıyor.
Geçtiğimiz hafta Avustralya’da muhalefet üyesi Barnaby Joyce, Çin’in elektrikli araçlardaki uzaktan erişim özelliklerini “kötü niyetli amaçlarla silah haline getirebileceği” uyarısında bulundu.
Bu kaygı, Avustralya’da satılan elektrikli araçların %80’inden fazlasının Çin’de üretilmesi (bu oran Tesla modellerini de kapsıyor) gerçeğine dayanıyor.
Gerçek ile bilim kurgu arasında
Siber güvenlik uzmanları, özellikle askeri alanlarda, Çin’in sürücülerin konum ve davranış verilerini toplayabilme olasılığına dikkat çekiyor. ABD’de ise bu tür “araç tabanlı casusluk” endişeleri, yabancı menşeli araç donanım ve yazılımlarının soruşturulmasına yol açtı.
Çin yapımı araçların gerçekten casuslukta kullanılıp kullanılmadığını anlamak için hükümetlerin daha derinlemesine inceleme yapması gerekiyor. Bu, karşı istihbarat önlemlerinin artırılmasını da içermelidir.
Araçların uzaktan devre dışı bırakılması mümkün mü?
Evet, bir aracın uzaktan devre dışı bırakılması teknik olarak mümkündür.
Ford, 2023 yılında uzaktan hizmet devre dışı bırakma teknolojisi için patent başvurusunda bulundu. Bazı GWM modelleri, izinsiz kullanım algılandığında aracı kilitleyen alarm ve immobilizer sistemlerine sahip. Ayrıca bazı üreticiler, çalınma sonrası araç takibi ve uzaktan durdurma hizmetleri sunuyor. Bu özelliklere sahip bir araç, teorik olarak kötü niyetli bir aktör tarafından hacklenebilir.
Gerçek bir örnek mi?
Yakın zamanda Çeçen lider Ramzan Kadirov, Elon Musk’ı, Ukrayna’da Tesla Cybertruck aracını devre dışı bırakmakla suçladı. Kadirov, Rus ordusunu destekliyor.
Bu iddia doğrulanmamış olsa da, yabancı bir aktörün uzaktan araçları hedef alabileceği olasılığına işaret ediyor.
Yine de Çin’in, bir ticaret anlaşmazlığı, siber çatışma veya konvansiyonel savaş sırasında araçları topluca devre dışı bırakması olasılığı, şimdilik distopik bir kurgu senaryosu gibi görünüyor.
Verilere kim erişiyor?
Sonuçta, devletlerin araçlardaki ileri teknoloji bileşenleri casusluk amacıyla kullanabileceği endişesi tamamen asılsız değil.
Modern, bağlantılı hizmetlere sahip bir araç satın aldığınızda, aslında şunu kabul ediyorsunuz:
“Araç kullanım verileri ve kişisel bilgiler, üreticiyle ve servis ağlarıyla paylaşılabilir.”
Ancak bir ürün satın aldığımızda, onun tam kontrolünün bizde olmasını bekleriz.
Gerçekte ise, bu kontrolün bir kısmı üreticiye ve veri servis sağlayıcılara geçiyor.
Gizlilik konusunda endişeli misiniz?
Eğer mahremiyet sizin için önemliyse, kontrolü elinize alın.
Bunun için:
- Aracınızın hangi bilgileri topladığını,
- Üreticinin bu verileri kiminle paylaştığını,
- Ve verilerin nerede, nasıl depolandığını öğrenin.
Bu farkındalık, hem kişisel güvenliğinizi hem de ulusal veri egemenliğini korumanın ilk adımıdır.
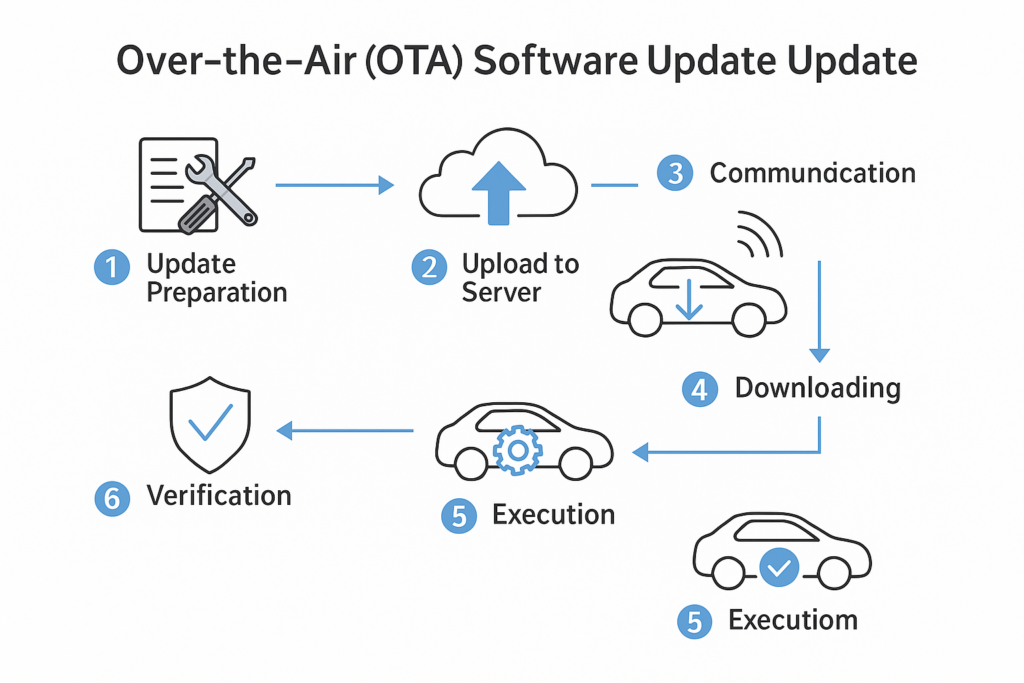
UNECE R156 Compliance Process and Vehicle Software Update Standards
Birleşmiş Milletler, R156 Uyum Süreci ve Araç Yazılım Güncelleme Standartları
Birleşmiş Milletler Regülasyonu No. 156 (R156) gayri resim Türkçe tercümesi.
☑️ Bu düzenleme, kara taşıtlarında Yazılım Güncelleme Yönetim Sistemleri (SUMS) için küresel standartları belirlemektedir.
R156, ister uzaktan (OTA), ister doğrudan erişim yoluyla olsun, yazılım güncellemelerinin güvenli, şeffaf ve sistematik bir şekilde yürütülmesini zorunlu kılmaktadır. Uyumluluk yalnızca teknik bir zorunluluk değil; hukuki ve etik bir sorumluluktur.
Otomotiv Over-the-Air (OTA) Yazılım Güncellemesi Süreci
1️⃣ Hazırlık (Preparation)
Üretici, güncelleme dosyasını geliştirir, test eder ve dijital olarak imzalar.
2️⃣ Sunucuya Yükleme (Upload)
Test edilmiş güncelleme paketi, üreticinin güvenli sunucusuna yüklenir.
3️⃣ Araç-Sunucu İletişimi (Communication)
Araç internete bağlanır ve güncelleme olup olmadığını kontrol eder.
4️⃣ İndirme (Downloading)
Güncelleme paketi araca kablosuz olarak (Wi-Fi, 4G, 5G) indirilir.
5️⃣ Yürütme (Execution)
Araç duruyorsa ve koşullar uygunsa, yazılım güncellemesi kurulur.
6️⃣ Doğrulama (Verification)
Kurulum sonrası doğrulama yapılır. Gerekirse eski sürüme geri dönülür (rollback).
R 156 kapsamında, bir araç tipinin yazılım güncellemeleriyle ilgili olarak tip onayı alabilmesi için karşılaması gereken başlıca gereklilikler şunlardır:
RXSWIN Ataması:
Araç tipi, tür onayı ile ilişkili yazılımı temsil eden RX Yazılım Tanımlama Numarası (RXSWIN) ile donatılmalıdır.
Yazılım Sürüm Tanımlama:
Her RXSWIN için geçerli olan tüm yazılım sürümleri ve bu sürümlere ait bütünlük doğrulama verileri (ör. hash, checksum) açıkça belgelenmeli ve takip edilebilir olmalıdır.
Yazılım Takibi ve Uyumluluk:
Araç üreticisi, RXSWIN’e sahip her araç için yazılım güncellemelerinin öncesi ve sonrasına dair bilgilerle birlikte uyumluluğu doğrulayabilmelidir.
Sistemler Arası Etkileşim:
Yazılım güncellemelerinin, diğer sistemlerle olan karşılıklı bağımlılıkları etkileyip etkilemediği değerlendirilmelidir.
Güncelleme Öncesi Kontrol:
Güncelleme uygulanmadan önce, hedef araç(lar)ın mevcut yapılandırmasının yeni yazılım sürümü ile uyumlu olup olmadığı doğrulanmalıdır.
Fonksiyonel Değişiklikler:
Güncelleme ile yeni işlevlerin eklenip eklenmediği, mevcut işlevlerin değişip değişmediği ya da devre dışı bırakılıp bırakılmadığı belgelenmeli; bu değişikliklerin mevzuata etkisi değerlendirilmelidir.
Tür Onayına Etki:
Güncellemenin, sistem tür onayı parametrelerini veya ilgili mevzuattaki herhangi bir hükmü etkileyip etkilemediği analiz edilmelidir.
Güvenli ve Yetkili Yürütme:
Güncellemenin, güvenli bir ortamda ve yalnızca yetkin kişiler tarafından yürütüldüğünden emin olunmalıdır. Özellikle özel beceri gerektiren işlemlerde bu husus kritik önemdedir.
Kullanıcıya Bilgilendirme:
Araç kullanıcısı, yazılım güncellemeleri hakkında zamanında ve yeterli düzeyde bilgilendirilmelidir.

We provided a briefing to the Foreign Police Liaison Officers Community on automotive cybersecurity and methods of automotive cyber attacks.

Identifying Hidden Signals and Deception via the Neck Area: Behavioral Reasons Behind Touching the Neck, Necklaces, and Watches in Men and Women
Interpretation of Gunshot Residue (GSR) Findings
Gunshot residues constitute important evidence in court proceedings involving firearm-related incidents; however, when evaluating such cases, gunshot residue findings must be supported by additional corroborative evidence.
Synthetic Identity Documents
Synthetic identities are artificial identity documents created to generate images that closely resemble genuine and authentic identity documents. These identities are designed to imitate the appearance of legitimate identification documents, including driver’s licenses, passports, and other official forms of identification.
Kaynak: Interpol
The Reliability of Metadata in Digital Forensic Analysis
Crime Scene Investigation Training Program (Ankara University Continuing Education Center (ANKUSEM)

Presentation on Automotive Cybersecurity and Deepfake Technologies Necmettin Erbakan University – Seydişehir Ahmet Cengiz Faculty of Engineering




Deepfake and Synthetic Media Timeline

Guidelines for Expert Witnesses and Standards to Be Included in Expert Reports
ECE R155 is a regulation issued by the United Nations Economic Commission for Europe (UNECE). This regulation establishes uniform provisions for the approval of vehicles with regard to cybersecurity and Cybersecurity Management Systems (CSMS). In addition, the regulation defines automotive cyberattack threats and methods, as well as the preventive measures that can be taken against them. For the unofficial full Turkish translation of the regulation, please contact us.
Automotive Cyber Attacks and Security Vulnerabilities: A Comprehensive List
KAYNAK ECE R 155
How Can Deepfakes Be Detected?
ECE R 155
ECE R155, Birleşmiş Milletler Avrupa Ekonomik Komisyonu'nun (ECE) 155 Sayılı Yönetmeliğini ifade eder. Bu yönetmelik, araçların siber güvenlik ve siber güvenlik yönetim sistemleri açısından onaylanmasına ilişkin yeknesak hükümleri ortaya koymaktadır. ECE R155, özellikle elektronik ve iletişim sistemlerine odaklanarak araçların siber güvenliğini sağlamaya yönelik gereklilikleri ve prosedürleri belirler. Yetkisiz erişim, veri manipülasyonu ve siber saldırılardan kaynaklanan potansiyel güvenlik tehlikeleri ile ilgili riskler de dahil olmak üzere, modern araçlardaki siber güvenlik tehditleriyle ilgili artan endişeleri gidermeyi amaçlamaktadır. Yönetmelik, araç üreticileri tarafından uygulanacak siber güvenlik yönetim sistemlerine (CSMS) ilişkin ilkeleri özetlemekte ve araç elektronik sistemleri ile iletişim arayüzlerinin güvenliğinin sağlanmasına yönelik teknik gereklilikleri belirlemektedir. Araçlar daha bağlantılı hale geldikçe ve elektronik sistemlere bağımlı hale geldikçe, ECE R155'e uyumluluk giderek daha önemli hale geliyor. ECE R155, araçların siber güvenliğini sağlamak ve siber güvenlik düzenlemelerinin farklı ülke ve bölgeler arasında uyumlaştırılmasını teşvik etmek için uluslararası bir standart olarak hizmet vermektedir. Tüketiciler için araçların emniyet ve güvenliğinin artırılmasına katkıda bulunmanın yanı sıra otomotiv endüstrisinin siber güvenlik zorluklarını çözme becerisine güven oluşturulmasına yardımcı olur. İngilizce Metin İçin: https://unece.org/transport/documents/2021/03/standards/un-regulation-no-155-cyber-security-and-cyber-security BM Düzenlemesi No. 156 - Otomotiv Yazılım güncelleme ve yazılım güncelleme yönetim sistemi İngilizce Metin İçin https://unece.org/transport/documents/2021/03/standards/un-regulation-no-156-software-update-and-software-update
ISI/SAE 21434:2021
ISO/SAE 21434:2021, Uluslararası Standardizasyon Örgütü (ISO) tarafından yayınlanan "Karayolu araçları – Siber güvenlik mühendisliği" başlıklı bir standarttır. Bu standart, otomotiv endüstrisinin araçlardaki elektrik ve elektronik sistemlerle ilgili siber güvenlik risklerini yönetmesine yönelik kılavuzlar ve öneriler sağlar. Araçların siber tehditlere karşı güvenliğinin sağlanmasına yönelik risk değerlendirmesi, siber güvenlik yönetimi, geliştirme süreçleri ve doğrulama yöntemleri gibi çeşitli hususları içerir. ISO 21434:2021, tasarım, geliştirme, üretim, işletme, bakım ve hizmetten çıkarma dahil olmak üzere otomotiv sistemlerinin yaşam döngüsü boyunca siber güvenlik mühendisliğine sistematik bir yaklaşım oluşturmayı amaçlamaktadır. Otomotiv endüstrisindeki üreticilerin, tedarikçilerin ve diğer paydaşların siber güvenlik önlemlerini süreçlerine ve ürünlerine etkin bir şekilde entegre etmelerine yardımcı olur. Standart, siber güvenliğin ürün geliştirmenin ilk aşamalarından itibaren ve bir aracın tüm yaşam döngüsü boyunca dikkate alınmasının önemini vurguluyor. Kuruluşlar, ISO 21434:2021'de belirtilen yönergeleri takip ederek otomotiv sistemlerinin siber saldırılara karşı dayanıklılığını artırabilir ve tüketiciler için araçların emniyetini ve güvenliğini sağlayabilir.
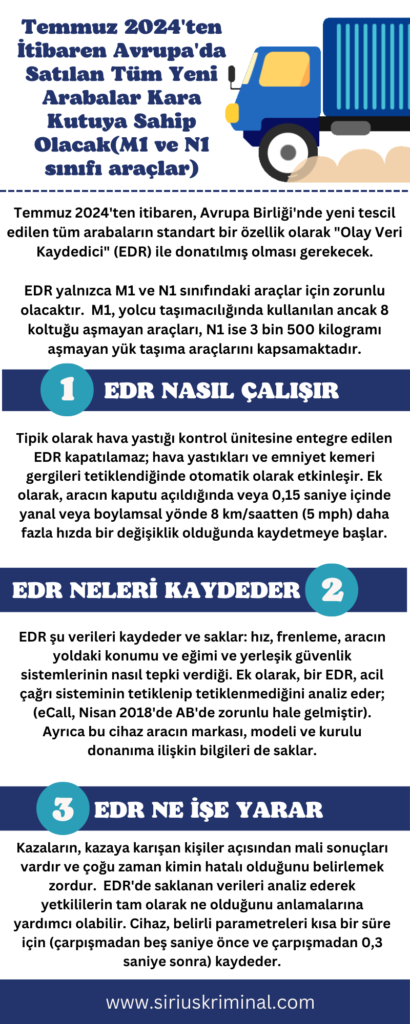
Automotive Event Data Recorder (EDR)
Modern Vehicles Are Exposed to Cyber Attacks
MODERN ARABALAR BİLGİSAYAR KORSANLARINA KARŞI KORUMASIZ
Mehmet ŞEN E. Emniyet Müdürü
Sirius Kriminal Kurucu Ortak
Bağlantı/Bağlanabilirlik ve Yazılım Tanımlı Mimarilerin entegrasyonu, Otomotiv ve Akıllı Mobil ekosisteminde devrim yaratarak; otonom sürüş, tahmine dayalı bakım ve gelişmiş bilgi-eğlence sistemleri gibi son teknoloji özellikleri mümkün kılmıştır. Ancak güncel ya da olası yenilikler bu ekosistemde önemli siber güvenlik sorunları da ortaya çıkarmıştır.
2023 yılı Otomotiv ve Mobil Siber Güvenlik ekosisteminde büyük ölçekli olaylara doğru dramatik bir değişime tanıklık etti. Upstream'in araştırmasına göre 2019-2023 yılları arasında, açık internette ifşa edilen olaylar yüzde 50 oranında artarak, 2023 yılında 295 raporlanan vakaya ulaşmıştır. 2023 yılında, yapılan saldırıların %95'i uzaktan ve %64'ü kötü niyetli (Siyah Şapkalı) bilgisayar korsanları tarafından gerçekleştirilmiştir.
Otomotiv siber saldırısı iki ana kategoriye ayrılabilir:
1- Uzaktan Saldırılar
a-Kısa menzilli (örn. ortadaki adam saldırısı) veya
b-Uzun menzilli (örn. API/Uygulama Programlama Arabirimi tabanlı saldırı)
2- Araca fiziksel bir bağlantı (örn. OBD/Araç İçi Teşhis Sistemi portu) gerektiren fiziksel saldırılar.
Uzaktan saldırılar ağ bağlantısına (örneğin Wi-Fi, Bluetooth, 3/4/5G ağları) dayanır ve çok sayıda aracı aynı anda etkileme potansiyeline sahiptir.
Otomotiv Siber Tehditleri, Temel Finansal Etkileri ve Araç Güvenliği
Uzaktan Araç Korsanlığı: Bilgisayar korsanları, bir aracın yazılımındaki veya iletişim protokollerindeki açıklardan yararlanarak elektronik kontrol ünitelerine (ECU'lar) yetkisiz erişim sağlayabilir ve frenler, direksiyon veya hızlanma gibi çeşitli sistemleri uzaktan manipüle edebilir. Bu durum potansiyel olarak kazalara veya araç hırsızlığına yol açabilir.
Anahtarsız Giriş ve Kontak Korsanlığı: Birçok modern araçta kablosuz sinyallere dayanan anahtarsız giriş ve ateşleme sistemleri kullanılmaktadır. Bilgisayar korsanları, anahtarsız giriş/marş motoru; röle; sinyal karıştırma ve API saldırı yöntemleri ile anahtara fiziksel erişim olmadan kapıların kilidini açmak, motoru çalıştırmak ve hatta aracı çalmak için bu sinyalleri kesebilir ve manipüle edebilir.
Bilgi-Eğlence Sistemi İstismarı: Bilgi-eğlence sistemleri genellikle Wi-Fi, Bluetooth veya hücresel bağlantılar gibi bağlantı özelliklerine sahiptir. Bilgisayar korsanları bu sistemlerdeki güvenlik açıklarından faydalanarak GPS konumları, arama kayıtları veya akıllı telefonlardan senkronize edilen kişisel bilgiler gibi araçta depolanan hassas verilere erişim sağlayabilir.
Konum takibi: Kullanıcı veya sahibinin izni olmadan bir aracın konumunu ve hareketini izlemek için GPS navigasyon verilerini kullanabilir.
Teşhis Portu İstismarı: Tamirciler tarafından araç arıza tespiti ve bakımı için kullanılan yerleşik arıza tespit (OBD-II) portu da bilgisayar korsanları tarafından istismar edilebilir. OBD-II portuna takılan kötü niyetli cihazlar potansiyel olarak aracın ağına erişim sağlayabilir ve kritik işlevleri kontrol edebilir.
Fidye Yazılımı Saldırıları: Siber suçlular fidye yazılımı saldırılarıyla otomotiv üreticilerini veya tedarikçilerini hedef alabilir, kritik sistemleri şifreleyebilir veya hassas verileri çalabilir ve bunların serbest bırakılması için ödeme talep edebilir. Bu durum üretim süreçlerini kesintiye uğratabilir veya müşteri verilerini tehlikeye atabilir.
Tedarik Zinciri Saldırıları: Otomotiv tedarik zincirleri, araç üretiminde kullanılan bileşenleri ve yazılımları sağlayan çok sayıda tedarikçiyi içerir. Bilgisayar korsanları bu tedarikçileri hedef alarak kötü amaçlı yazılımlar yerleştirebilir veya daha sonra araçlara entegre edilebilecek bileşenleri tehlikeye atarak önemli siber güvenlik riskleri oluşturabilir.
Veri Gizliliği İhlalleri: Bağlantılı araçlar, sürücüler, yolcular ve araç operasyonları hakkında hassas bilgiler de dahil olmak üzere büyük hacimlerde veri üretir ve iletir. Siber saldırılar yoluyla bu verilere yetkisiz erişim, gizlilik ihlallerine, kimlik hırsızlığına veya bireylerin hareketlerinin izinsiz takibine neden olabilir. Bir tehdit aktörü fikri mülkiyet (IP), ticari sırlar, finansal bilgiler veya kişisel olarak tanımlanabilir bilgiler (PII) gibi özel, gizli verilere yetkisiz erişim sağladığında bir veri ihlali meydana gelir. Veri ihlallerini içeren siber güvenlik vakaları en yaygın ve en pahalı vakalardır.
Siber Güvenlik ile ilgili Yasal ve Düzenleyici Uyumluluk İhlalleri: Yasa, yönetmelik veya endüstri standartlarının ihlaline yol açan siber tehditler ve saldırılar firmaların dava edilmesine ve para cezaları ödemesine yol açabilir.
Dolandırıcılık: Bir kişi veya kuruluş tarafından kişisel veya mali kazanç için kötü niyetle gerçekleştirilen kimlik hırsızlığı, kilometre sayacının kurcalanması ve hesap korsanlığı gibi aldatıcı eylemler korsanlar ve dolandırıcılar tarafından kullanılabilir
Elektrikli araç (EV) Şarj İstasyonları Güvenlik Açıkları: Bu güvenlik açıkları, şarj işlemlerini aksatmak, elektrik çalmak, kişisel verileri çalmak (Şarz Cihazları: kullanıcı kimlik bilgileri, şarj oturumu ayrıntıları ve konum bilgileri dahil olmak üzere hassas verileri toplar ve depolar), şarj ağının bütünlüğünü tehlikeye atmak veya şarj ağına yetkisiz erişim sağlamak için kötü niyetli kişiler tarafından potansiyel olarak kullanılabilir. Ayrıca elektrikli araç şarj altyapısında kullanılan bileşenler ve yazılımlar birden fazla tedarikçi ve üreticiden temin edilebilir. Bu bileşenlerdeki güvenlik açıkları veya tedarik zincirindeki tehlikeler, şarj altyapısına güvenlik riskleri getirebilir. Bunların yanı sıra Hizmet Reddi (DoS) saldırıları ile elektrikli araç şarj ağları, kötü niyetli aktörlerin ağı aşırı trafik veya taleplerle boğduğu ve şarj altyapısını meşru kullanıcılar için kullanılamaz hale getirdiği DoS saldırılarına maruz kalabilir.
Araçta Her Şeye Bağlı (V2X) Saldırıları: Araçtan her şeye bağlı (V2X), araçlara olanak sağlayan teknoloji için kullanılan ortak bir terimdir, altyapı ve diğer aktif yol kullanıcılarının sürekli iletişim halinde olmalarını sağlamak için mevcut hücresel ağ altyapısı olarak tanımlanabilir. Araç bağlantısının yedi temel modu vardır: Araçtan Altyapıya (V2I), Araçtan Araca (V2V), Araçtan Ağa (Trafik Işıklar vb. V2N), Araçtan Buluta (V2C), Araçtan Yayaya (V2P), Araçtan Cihaza (Şarz İstasyonu vb. V2D), Araçtan şehir elektrik şebekesine (V2G). Bu bağlantılara kullanarak yapılabilecek saldırılar emekleme aşamasındadır, ancak önümüzdeki yıllarda çok daha sık hale gelecektir.
Yukarıda belirtilen siber saldırılardan sonra yapılan yaygın olumsuz basın haberleri tüketici ve yatırımcı güvenini aşındırır ve kamuya açıklanan siber olayların finansal değerleme (piyasa değeri), güven ve algı üzerindeki olumsuz etkisi itibarın zedelenmesine neden olur. Ek olarak, bir aracın yazılım bileşenlerindeki siber güvenlik açıkları, üreticilerin sorunları güncellemek ve çözmek, etkilenen araçların güvenliğini ve düzgün çalışmasını sağlamak için geri çağırma yapmasını gerektirebilir ve bu da firmalar için çok büyük mali yükümlülükleri ortaya çıkmasına sebep olabilir.
Siber saldırılar Otomotiv, Akıllı Mobil Sistemler ve Hizmet Olarak Mobilite (MaaS) ekosisteminin her segmentini tehdit etmektedir:
1- Orijinal Ürün Üreticileri,
2- Yedek Parça Tedarikçileri
3- Araç Yazılım ve Donanım Tedarikçileri
4- Elektrikli araçlar
5- Elektrikli Şarj İstasyonları ve Elektrik Şebekesi
6- Otonom Araçlar
7- Tarım Makineleri
8- Mobil Nesnelerin İnterneti
9- Telematik Servis Sağlayıcılar
10- Filo Yönetimi
11- Araç Satış Bayileri
12- Araba, Ticari ve Teslimat Filoları
13- Toplu Taşıma ve Kamu Filoları
14- Acil Servisler
15- Araç ve Motor Paylaşım Platformları
16- Araç Kiralama Şirketleri
17- Araç Paylaşım Platformları
18- Akıllı Şehirler
19- Sigortacılık Firmaları
Bilgisayar Korsanları Karanlık ve Derin İnterneti kötü emelleri için kullanmaktadır, bunun yanı sıra profesyoneller ve kullanıcıların ana platformu haline gelen sosyal medya da tehdit aktörlerinin dakikalar içinde milyonlarca insana ulaşmasına olanak sağlamaktadır.
Üretken yapay zekâ, programcılar ve üreticiler için yeni olanaklar sağlarken, saldırı ortamlarını simüle etmek için Üretici Yapay Zeka kullanıldığında, daha öngörülemez ve sofistike saldırılara yol açtığı için siber güvenlik uzmanları ek bir zorlukla karşı karşıya kalmaktadır.
Son zamanlarda popüler olan ve önümüzdeki yıllarda daha çok yaygınlaşması beklenen otonom araçlar, teknik açıdan bakıldığında, yeni sensör türleri, yazılım ve donanım işlevleri, hizmetler ve iletişim türleri potansiyel güvenlik açıklarını ortaya çıkararak gelecekte bir saldırı olasılığını artırmaktadır. Otonom araçlar, internet ve uydular da dahil olmak üzere birden fazla kaynaktan veri ve yön alan navigasyon sensörleriyle (örneğin GPS, LIDAR, kameralar, milimetre dalga radarı, IMU) donatılmıştır ve bu yapılar önlem alınmazsa siber saldırılara karşı oldukça korumasızdır.
Örnek Olaylar:
Haziran 2023'te, önde gelen Tayvan merkezli bir yarı iletken üreticisi, bir fidye yazılımı grubu ve BT donanım tedarikçilerinden birinin dahil olduğu ve sistemin ilk kurulumu ve yapılandırmasıyla ilgili bilgilerin sızmasına yol açan bir siber güvenlik olayını kamuoyuna duyurdu. Saldırganlar, gizli bilgiler içeren dahili belgelere erişim elde ettiklerini iddia ederek, verilerin şifresini çözmek ve çevrimiçi olarak yayınlanmasını önlemek için 70 milyon dolarlık bir fidye talep ettiler- bu da tarihteki bilinen en büyük fidye talebi haline geldi. İhlal birden fazla otomotiv paydaşını etkileyebilecek olsa da şirket, tedarikçisindeki siber olaydan ne ticari faaliyetlerinin ne de müşteri bilgilerinin etkilendiğini bildirdi. Şirket ayrıca olayın ardından bu tedarikçiyle olan veri alışverişini derhal sonlandırdı.
Bir yıl önce, Amerika Birleşik Devletleri Wisconsin Eyaleti, Milwaukee şehrinde çoğunlukla Koreli bir araç firmasından yapılan araba hırsızlıklarında önemli bir artış görüldü ve şüpheli hırsızların çoğu araba kullanmak için çok gençti. Sosyal medyada, gençlerin bu arabalarla gezintiye çıktıklarını gösteren videolar ortaya çıktı- hız yapıyorlar, yoldan çıkıyorlar ve bazen camlardan sarkıyorlardı. Bu hırsızların amacı arabalardan parça söküp satmak değil, sosyal medyada nüfuz ve izlenme kazanmaktı. Araçların nasıl çalındığını gösteren videolar yayıldıkça, Koreli aracın hırsızlıkları ülke çapında arttı ve bunun üzerine Ocak 2023'te, Amerika'nın en büyük otomobil sigortacılarından ikisi, çalınması kolay bulunduğu belirlediği bu araçlar için belirli şehirlerde poliçe yazmayı reddetti.
Kaynak: 1-Açık İnternet Kaynakları
2- Upstream Global Automotive Cybersecurity Report 2024
Automotive Cyber Attack Methods

Judicial Decisions of the Turkish Court of Cassation Regarding Y-STR Analysis
Y STR KROMOZON İLE İLGİLİ YARGITAY KARARLARI (T.C. YARGITAY 2. Hukuk Dairesi Esas No: 2023/1719 Karar No: 2023/3075 Karar Tarihi: 07-06-2023) “Mahkemece yapılan yargılama sırasında Adli Tıp Kurumuna yazılan müzekkereye verilen cevabi yazı ile anne ve baba olduğu iddia edilen şahıslar olmaksızın, hangi cinsiyetten olursa olsun kardeş (aynı anne ve babadan) olduğu iddia edilen şahıslara ait biyolojik örneklerin çalışılması ile kardeşlik yönünde DNA incelemesi yapmak teknik olarak mümkün olmadığı, erkek cinsiyetli davalı ve davacılardan, Y STR DNA incelemesi ile bu şahısların aynı babasal soydan gelip gelmediklerine yönelik inceleme yapılması teknik olarak mümkün olduğunu, yapılacak bu değerlendirme babalık bir kardeş oldukları hakkında bilgi vermeyeceğini sadece erkek soyundan gelen erkek bireyler arasında aynı soydan geldiklerinin tespitinin yapılabileceğinin belirtilmesine dair müzekkere cevabı üzerine ... Büyükşehir Belediye Başkanlığı Mezarlıklar Daire Başkanlığı'na yazı yazılarak mezara ilişkin adres bilgilerinin istenildiği, ancak ... TC. Kimlik numaralı 24.02.1962 tarihinde vefat eden ...'ın defnedildiği mezara ilişkin herhangi bir kayda ulaşılamadığı, bu nedenle ... Adli Tıp Kurumu Başkanlığı'na yazı yazıldığı kardeşler arasında DNA incelemesi ile tarafların kardeş olup olmadığı hususunun sorulduğu, anne ve baba olduğu iddia edilen şahıslar olmaksızın, hangi cinsiyetten olursa olsun kardeş olduğu iddia edilen şahıslara ait biyolojik örneklerin çalışılması ile kardeşlik yönünde DNA incelemesi yapmanın teknik olarak mümkün olmadığı belirtilmiş, davacıların sunduğu nüfus kaydından ve salt tanık beyanları dikkate alınarak soybağı ilişkisi ispatlanamayacağından davanın reddine karar verilmiş, istinaf incelemesi neticesinde Bölge Adliye Mahkemesince istinaf başvurusunun esastan reddine karar verilmiştir. Nüfus kayıtlarının düzeltilmesi ve nüfus kayıtlarına yönelik tespit davaları kamu düzeni ile yakından ilgili bulunduğundan, hâkim istemle bağlı kalmayarak kendiliğinden de yapacağı araştırma ile elde edeceği sonuçlara göre karar vermek zorundadır. Somut olayda davalılardan bir kısmının Mahkemeye hitaben verdiği beyan dilekçesinde davacıların babası ile baba bir kardeş olduklarını beyan etmiş olmasına karşın Adli Tıp kurumunun cevabı yazısında belirtildiği şekilde erkek cinsiyetli davalı ve davacıların biyolojik örnekleri çalışılarak aynı baba soyundan geldiğinin tespiti için DNA tespiti yapılmaksızın ve davacıların nüfus kayıtlarında dedesi olarak görülen ve mezar yeri bilinen ...'a ait mezarda yapılacak fethi kabir sonucu alınacak örnekler ile davacılar ile kayıtta dedesi olarak bilinen kişinin gerçekten aynı soydan gelip gelmediklerinin tespiti ile tüm deliler birlikte değerlendirilerek sonucu uyarınca bir karar verilmesi gerekirken yazılı şekilde eksik inceleme ile karar verilmesi doğru olmayıp bozmayı gerektirmiştir.” (T.C. YARGITAY 8. Hukuk Dairesi Esas No: 2021/407 Karar No: 2021/4097 Karar Tarihi: 18-05-2021) “İddiaya dair DNA incelemesi yapılabilmesi için Şefaatli Asliye Hukuk Mahkemesi'ne talimat yazıldığı, talimat mahkemesince ... ile eşi ... ...'nın mezar yerlerinin tespiti için mahallinde keşif yapıldığı ve mezarların bulunduğu köyde 2000 ve 2010 yıllarında yaşanan sel felaketi sonrası mezarlığı da sel sularının bastığı ve mezar yerlerinin kaybolduğu ve ... ile eşi ... ...'nın mezar yerlerinin tespitinin mümkün olmadığının saptanması üzerine davacıların murisleri ... (...)'in, ..., ... ... ve ... ile ... ...(...), aynı anne babadan gelme kardeş olup olmadıkları, (otozomal STR DNA analiz çalışmaları ile mitokondriyel DNA analiz çalışması yapılmak suretiyle ), hususunda Adli Tıp Kurumu Biyoloji İhtisas Dairesince bu kişilerden alınan örnekler üzerinde çalışma yapılmış ve 26.09.2019 tarihli rapora göre; "Mitokondriyal DNA, sadece anneden çocuğa aktarılıp ve annesel soyağacındaki bireylerde (kardeşler, anneanne, teyze ve dayılar ile teyze çocukları gibi) aynı baz dizilimine sahip olduğundan, şahısların aynı annesel soydan gelip gelmedikleri ile ilgili bilgi sağlayabilir. İnceleme yapılan örneklerin mitokondriyal DNA'sının yüksek oranda polimorfizm gösteren HV1 bölgesindeki 16141-16521 arasındaki bazları / HV2 bölgesinin 31-400 arasındaki bazlarının yapılan incelemelerinde; ..., ... ..., ... ..., ... ve ...'ye ait mitokondriyal DNA dizilerinin birbiriyle uyumlu olduğu tespit edildi. Elde edilen sonuçlara göre ..., ... ..., ... ..., ... ve ...'nin aynı anne soyundan gelen bireyler olabileceği tespit edildi. ... ... ... Ve ...'ye ait YSTR DNA profillerinin birbiriyle uyumlu olduğu tespit edildi (Sadece erkek bireylere özgü olan Y kromozomu babadan oğula değişmeden aktarılır. Aynı soy ağacındaki erkek bireyler Y kromozomlarının mutasyona uğraması dışında aynı Y-STR DNA profiline sahiptir)” (T.C. YARGITAY 18. Hukuk Dairesi Esas No: 2015/1944 Karar No: 2015/15735 Karar Tarihi: 03-11-2015) “Dava Türk Medeni Kanunu'nun 301. ve devamı maddeleri uyarınca çocuk tarafından açılan babalığın tespitine ilişkindir. Mahkemece, davanın kamu düzenini ilgilendirmesi bakımından kuşku ve duraksamaya neden olmaksızın soybağının doğru olarak tespit edilmesi zorunludur. Öncelikle baba olduğu iddia edilen ………………’in mezarının tespit edilip fethi kabir yapılarak DNA incelemesine esas doku ve kemik örnekleri alınması, bu imkanın kullanılamaması halinde davacı ile kardeş olduğu iddia edilen davalılar arasında kardeşlik bağının olduğunu (aynı soydan geldiklerini) kanıtlar nitelikte DNA incelemesi yaptırılması ve alınacak rapor ile tarafların diğer delilleri birlikte değerlendirilip oluşacak sonuca göre bir karar verilmesi gerekirken eksik inceleme ve yerinde olmayan gerekçe ile davanın reddine karar verilmiş olması doğru görülmemiştir.” (T.C. YARGITAY 8. Hukuk Dairesi Esas No: 2018/16042 Karar No: 2020/928 Karar Tarihi: 05-02-2020) “Kamu düzeni ile yakından ilgili olan soybağının tespiti davalarında, Mahkemece, kuşku ve duraksamaya neden olmaksızın soybağının doğru olarak tespit edilmesi zorunludur. Öncelikle baba olduğu iddia edilen ...'ın mezarının tespit edilip fethi kabir yapılarak DNA incelemesine esas doku ve kemik örnekleri alınması, bu imkanın kullanılamaması halinde nüfus kaydına göre baba olduğu iddia edilen ... ile babalık bağı bulunan davalı ... ve davacı ... arasında baba yönünden kardeşlik bağının olduğunu (aynı soydan geldiklerini) kanıtlar nitelikte DNA incelemesi yaptırılması ve alınacak rapor ile tarafların diğer delilleri birlikte değerlendirilip oluşacak sonuca göre bir karar verilmesi gerekirken, DNA testi yaptırılmadan, nüfus kayıtlarına göre baba olduğu iddia edilen Havle ile davacının kardeş olduklarına dair rapor ve verilen tespit kararı ile davacı beyanları, bir kısım davalıların kabul beyanı ve tanık ifadeleri yeterli bulunarak davanın kabulüne karar verilmesi doğru görülmemiştir.” (T.C. YARGITAY 2. Hukuk Dairesi Esas No: 2023/6484 Karar No: 2023/5870 Karar Tarihi: 30-11-2023) “Nüfus kayıtlarının düzenli ve gerçeğe uygun olarak tutulması kamu düzeni ile yakından ilgilidir. Nüfus kayıtlarının düzeltilmesine ilişkin davalarda, mahkemelerin hiçbir kuşku ve duraksamaya neden olmaksızın doğru sicil oluşturmak zorunluluğu bulunmaktadır. Bu bakımdan hakim resen araştırma ilkesinin sonucu olarak kendiliğinden delil toplama yetkisine sahiptir. Mahkemece, bozma ilamı gereği annelik iddiası ile ilgili olarak DNA testi yapılması için ...'ın mezar yerinin tespit edilemediği, salt kolluk araştırması ve taraf beyanlarına göre yapılan tespitin nufüs kayıtlarının düzeltilmesine yeterli olmayacağı gerekçesi ile davanın reddine karar verilmiş ise de davacı vekili tarafından temyiz dilekçesi ekinde ...'ın mezar yerinin tespit edildiğine dair mezarlık ismi, mezar yerinin krokisi ve mezarlığın resmi sunulmuştur. Mahkemece belirtilen mezarın ...'a ait olup olmadığı yönünde tespit yapıldıktan sonra mezarda yapılacak fethi kabir sonucu alınacak örnekler ile DNA incelemesi yapılarak diğer tüm deliller birlikte değerlendirilip sonucuna göre karar verilmek üzere hükmün bozulması gerekmiştir.”
INTERPOL Issues a Warning to Law Enforcement Authorities:
The Impact of the Virtual Universe on Criminal Investigation Techniques
Bölüm I
- Kolluk Tarafından Verilen Hizmetlerin ve İhbarların Metaverse Ortamında Yapılması
- Metaverse’de Olay Yerinin Korunması ve Adli Analizlerde Kullanımı
Bölüm II
- Meta Suçlar
Bölüm III
- Metaverse’de Adli Bilişim
Bölüm IV
- Metaverse Yönetimi ve Yönetişimi
Sonuç
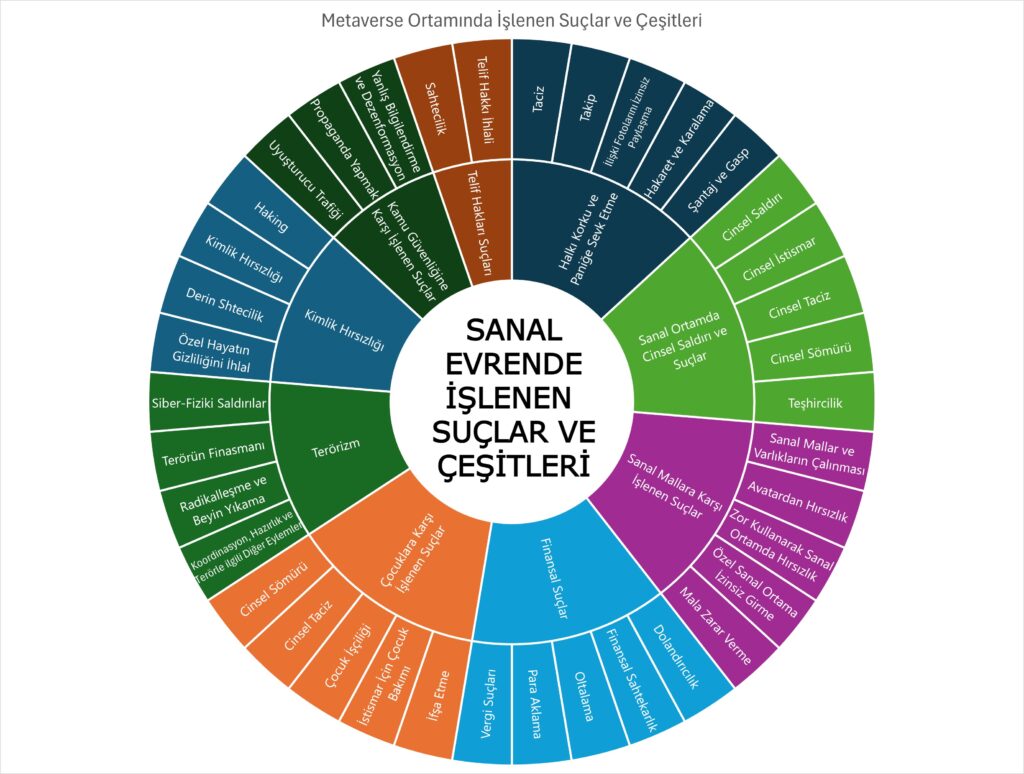
A Typology of Crimes in Virtual Environments
In order to update and harmonize existing classifications of crimes and harms, the diagram below illustrates a typology of certain crimes and potential harms emerging in the virtual universe. Some of these meta-crimes may extend into the real world. The World Economic Forum emphasizes that harms occurring in the virtual universe may be local or culturally specific, just as they are in the physical world. In addition, the virtual universe introduces spatial harms—such as gestures, postures, and digital assets—that will require a distinct and specialized approach.
Kaynak: INTERPOL, GÜVENLİK KUVVETLERİ BAKIŞ AÇISINDAN METAVERSE, Vaka, Suç, Adli Bilişim, Soruşturma, Yönetişim, Ocak 2024, Bilgilendirici Belge
Core Principles of Forensic Science
Adli Bilimlerin İlke, Prensip ve Kanunları
Mehmet ŞEN, Emekli Emniyet Müdürü, Olay Yeri İnceleme Uzmanı
Adli bilim, suç faaliyetlerinden veya hukuki veya idari davalardan kaynaklanan izleri incelemek için bilimsel bir süreç ve teknik yaklaşımlar uygulayan bir yöntemdir. Kriminalistik olarak da bilinen adli bilimler, hukuk mahkemelerinde ortaya çıkabilecek şüpheli sorulara yanıt bulmak için doğa bilimlerinin yasa ve ilkelerini kullanarak fiziksel kanıtların tanınması, belirlenmesi, bireyselleştirilmesi ve değerlendirilmesiyle ilgilenen bilimsel bir disiplindir. Adli bilimin bu ilkeleri, bir suçun ortaya çıkmasından sanığın mahkemede mahkûm edilmesine kadar olan ceza yargılamaları üzerinde doğrudan etkiye sahiptir.
Adli bilimin ceza yargılamasında önem taşıyan ilkeleri şunlardır:
________________________________________
1-Locard’ın Değişim Prensibi (Değişim Yasası)
Bu ilke Fransız bilim adamı Edmond Locard'a atfedilir. Teorileri, suçun önlenmesini ve toplumsal sonuçları birleştiren Kriminoloji, suç davranışının ve bunun hukuk sistemiyle olan etkileşimlerinin inceler. Adli bilimin temel ilkesini ortaya koyan adli bilim öncüsü ve kriminolog olan Locard: “Her temas bir iz bırakır.” sözü ile adli bilimin temel yasalarından birini belirlemiştir ve olay yerinde birçok iz kaldığını ve bunların uygun şekilde yorumlanması halinde en değerli bilgileri elde edilebileceğini öne sürmüştür.
“Herhangi iki nesne birbiriyle temas ettiğinde, aralarında her zaman çok küçük parçacıklar alışverişi olur”.
Bu prensibe göre, suçlunun veya suçun işlenmesinde kullandığı silahın mağdurla veya onun çevresi/nesneleriyle teması halinde o mahalde iz bırakabilmektedir. Aynı şekilde suçlu veya silahları da aynı temastan izler taşıyabilmektedir. Başka bir örnek olarak trafik kazasında çarpıp kaçma olayında çarpıp kaçan araçta kan lekelerinin varlığı söz konusudur. Aynı şekilde mağdurun üzerinde ve çevresinde de lastik izleri, ayakkabı izleri, araç boyaları bulunacaktır. Bir başka klasik örnek ise tecavüz mağdurunda bulunan kan/meni lekesi, zanlının vücudunda ise mağdurun saç varlığının görülmesidir.
Bu kanun bilimsel suç soruşturmasının temelini oluşturmaktadır. Bu prensip, parmak izleri, lastik izleri, atış artıkları, ayak izleri, saç örnekleri, cilt kalıntıları, kaslar, vücut sıvıları, kan, giysi parçaları vb. gibi temasın olduğu tüm durumlarda doğrulanır. DNA analizi bu prensibin basit bir uygulamasıdır ve analiz altında olan bulguların faile ait olduğuna inanılmaktadır.
2- Bireysellik Yasası
Bu ilke Paul L Kirk'e (1963) atfedilir ve adli bilimin yapı taşlarında biri olarak kabul edilir. Bu yasa, ister kişi ister nesne olsun, her varlığın benzersiz ve bireysel olduğunu ifade eder. Doğal ya da yapay hiçbir şey aynı olamaz. Tanrı'nın tohumlar, meyveler ve bitkiler gibi yarattıkları bile benzersizdir. Örnek: Banknotlar, madeni paralar, daktilo yazıları vb. aynı veya benzer görünmelerine rağmen benzersizdir.
Kirk, adli bilimin tek bir kaynaktan geldiği düşünülen iki öğenin (sorgulanan ve bilinen veya iz ve örnek) kaynağına odaklandığını iddia eder. Dolayısıyla kimliklendirme, iki şeyin aynılığından ziyade, olay yerinde bırakılan izlerden bireysellik oluşturmakla ilgilidir. Bu, izlerin ve örneklerin analiz edilmesi yoluyla tanımlamanın dolaylı olarak gösterilebileceği anlamına gelir; örneğin hiçbir iki parmak izi aynı değildir.
3- Sürekli Değişim Yasası
Sürekli değişim yasasına göre, “Zaman içerisinde her şey değişir. Yani kalıcı ve değişmez hiçbir şey yoktur.”
Sürekli değişim yasasının cezai soruşturma üzerindeki etkisi çok büyüktür. Suçlular zaman geçtikçe süregelen bir değişime maruz kalırlar. Suçlu zamanında yakalanmazsa; parmak izleri, kan lekelerinden alınan kan grupları ve DNA profili dışında kalan deliller ile ilgili tespit edilemez hale gelir. Ayrıca olay yerinde de hızlı bir değişim yaşanır, güvenliğin sağlanmaması durumunda olay yeri tespit edilemez hale gelir ve fiziksel delillerin kaybolması, tahrif edilmesi veya yok edilmesi ihtimali vardır.
4- Karşılaştırma Yasası
Farklı numuneler yalnızca benzer numunelerle karşılaştırılmalıdır. Başka bir deyişle, kan örnekleri diğer kan örnekleriyle, lifler de diğer liflerle karşılaştırılır ve bu böyle devam eder.
Karşılaştırma Yasası "yalnızca benzerlerin karşılaştırılabileceğini" belirtir. Veya “Karşılaştırma ancak benzer olduğunda mümkündür.”
Örneğin, olay yerinde bulunan bir kovan, ateşli silahla (tabanca) kıyaslanabilir ama pompalı tüfekle karşılaştırılamaz; Duvara yazılan yazı incelenirken kâğıt üzerindeki yazıyla değil, duvardaki benzer yazıyla karşılaştırılması gerekir. Bunun nedeni, herhangi bir kişinin kâğıda veya duvara yazdığında boyut ve hizalamaların değişebilmesidir.
5- Analiz Yasası
Analiz yasası, tahrifat ve imhayı önlemek amacıyla, analiz için doğru numunelerin öngörülen şekilde toplanması ve saklanması ile ilgilidir. Bunun nedeni, şüphesiz herhangi bir analizin kalitesinin, analiz altındaki numunenin kalitesine, delil teslim zincirine ve analistin uzmanlığına göre belirlenmesidir.
Bu ilke, “Analiz, numune analizinden daha iyi olamaz” veya “Analizin, uzmanlar tarafından doğru analiz yapılması için uygun numune alımı (doğru numune alma ve paketleme) ile yapılması gerekir” şeklinde ifade edilmektedir.
Örneğin: meni lekesi analizi durumunda, soruşturma memurunun kanlı elbiseleri toplamasının hiçbir faydası olmayacaktır. Patlayıcı maddenin test edilmesi gerektiğinde, patlama mahallinden toplanan ve patlamanın materyalist maddesini taşıyan artık malzemeler olmalıdır (patlayıcının kimliğini tespit etmek için tek başına toprağı test etmenin bir faydası olmayacaktır).
6-Olasılık Yasası
Tüm tespitler ve kimliklendirmeler bazen bilinçli ya da bilinçsiz olarak koşullara bağlı olarak doğrudur. Ayrıca adli analizden elde edilen sonuçlar, kullanılan yönteme ve bu yöntemin avantaj ve dezavantajlarına bağlıdır. Bunların dikkate alınması gerekir.
Bu ilke, "kesin veya belirsiz tüm tespitlerin bilinçli veya bilinçsiz olarak olasılığa dayalı olarak yapıldığı" gerçeğine dayanmaktadır.
Olasılık, belirli bir olayın, olayın gerçekleşebileceği çeşitli yollardan belirli bir şekilde meydana gelme şansını belirleyen matematiksel bir kavramdır. Örnek olarak burun hızması ve sağ kolunda dövme izi bulunan gözlüklü bir kadının cesedinin kimliğinin tespit edilmesi durumu verilebilir.
Sonuç olarak adli analiz, izlerin bulunmasına ve bunların bireylere bağlanmasına bağlıdır. Olay yerinde herhangi bir ize rastlanmaması durumunda şüphelilerin tespit edilmesi mümkün değildir. Ancak iz bulunması halinde, bunların uygun şekilde analiz edilmesi ve sonuçların uygun şekilde yorumlanması şartıyla delil olarak kullanılabilir.
7- İkinci Derece Gerçekler Kanunu
İlke şu ifadeye dayanmaktadır: "Gerçekler asla yalan söylemez, ancak insanlar yalan söyleyebilir."
Bu, görgü tanıklarının ifadeleri, mağdur ifadeleri vb. ile ilgilidir. İnsanlardan kanıt sunmaları istendiğinde, sundukları kanıtların hatalı olma ihtimali vardır. Bu kasıtsız (yanlış gözlemler yaparak, varsayımlarda bulunarak) veya kasıtlı (yalan söyleyerek veya abartarak) olabilir. Bunun aksine, gerçeklere ve delillere dayalı bir açıklama sunan (soruşturmaya dayalı) kanıtların doğru olma şansı daha yüksektir ve daha güvenilirdir.
Dolayısıyla Adli Bilim, ceza adaletinin idaresi amacıyla doğa bilimlerinin ilke ve yöntemlerini uygulayarak fiziksel delillerin elde edilmesine (tanımlanması), tespitine, bireyselleştirilmesine ve değerlendirilmesine yönelik bilimsel bir disiplindir.
Kaynak: https://simplyforensic.com/fundamentals-of-forensic-science/principles-of-forensic-science/
Trends in Cybercrime Growth and Associated Costs

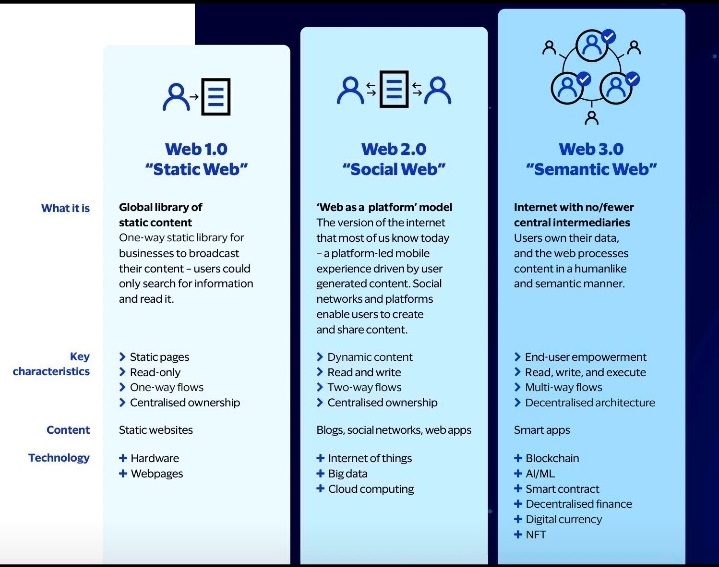
WEB 1.0 WEB 2.0 WEB 3.0 KARŞILAŞTIRMASI
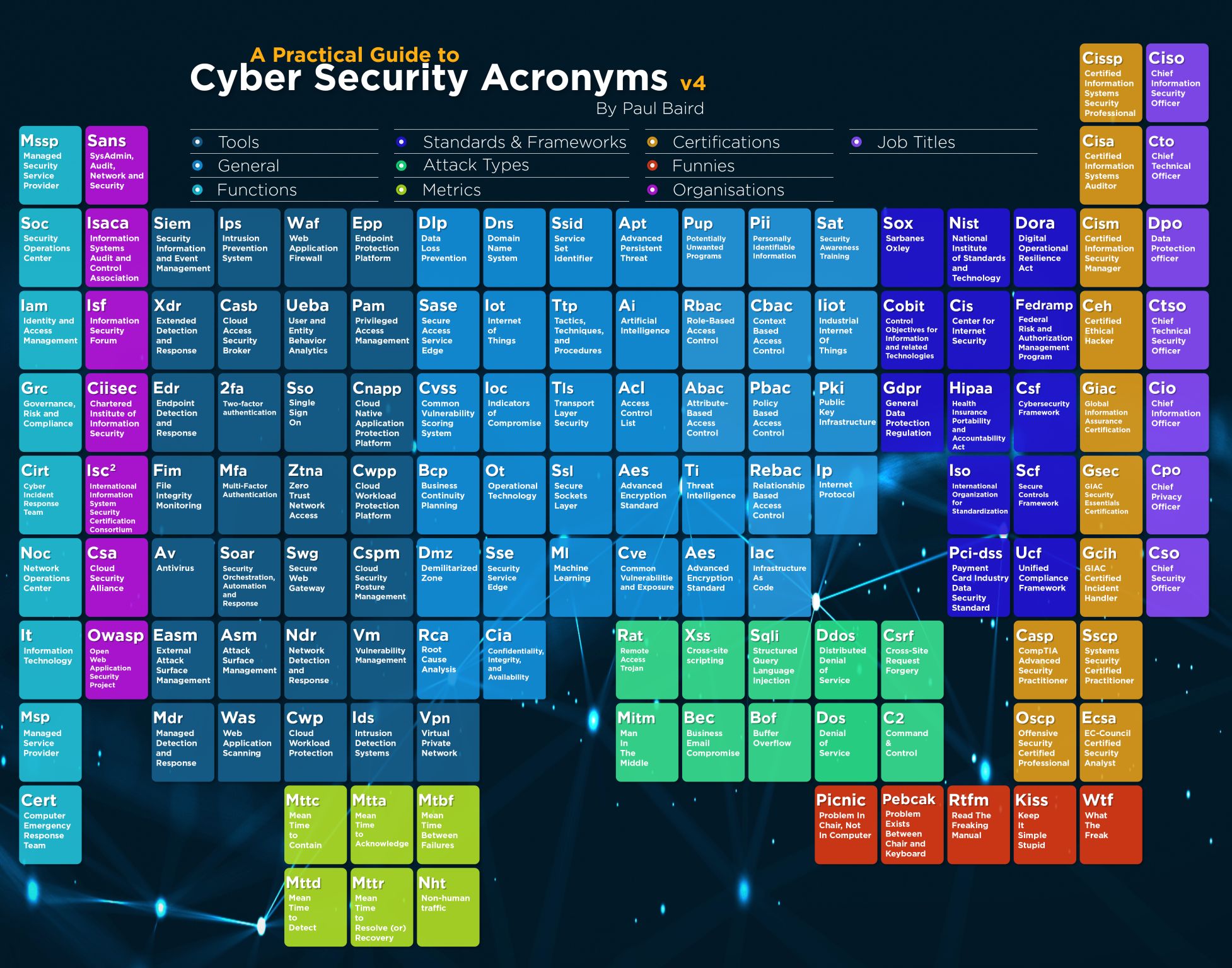
Cyber Security Acronyms
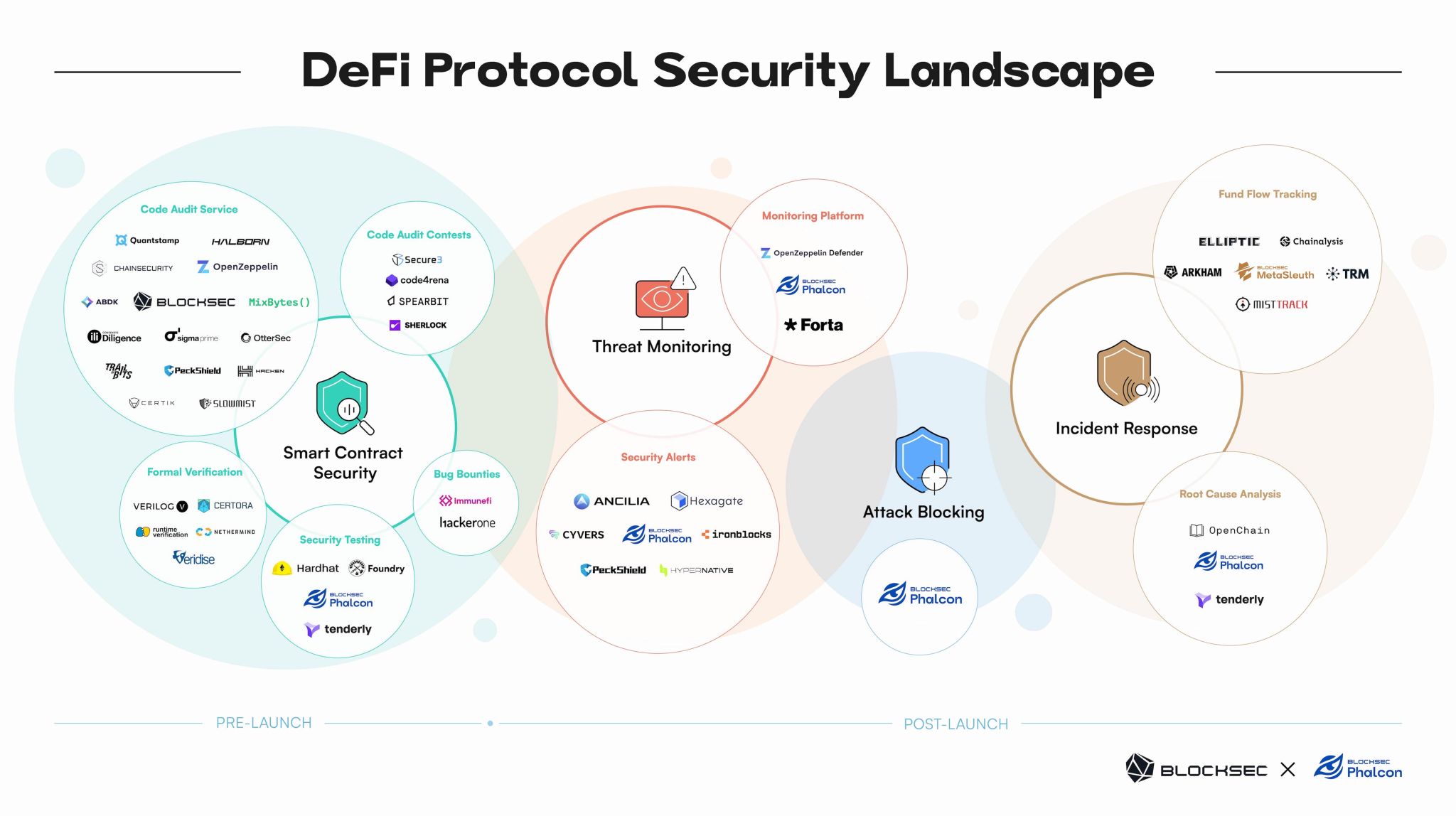
Security Landscape of Decentralized Finance (DeFi) Protocols
Quantum-Based Encryption
Why Is Quantum-Based Encryption Important to Protect Files Against Data Breach?
Without questioning the measures companies take to arm themselves against cybercrime, it is all too common for companies, despite all efforts made, to fall victim to malware and ransomware.
Thinking it won't happen to you because you employ or have hired the best cybersecurity specialist is a mistake many make. There is no 100% guarantee of cyber security because where people are involved, mistakes can be made. And small mistakes can have large consequences; in other words, security is only as good as its weakest link!
Of course, you can close and barricade all ports so no one can enter, but that usually has the consequence that working on the network entails the necessary inconveniences.
What you can do, is secure the data in such a way that cybercriminals cannot use it. Data they can't read is worthless to them. Exerting blackmail by threatening that your data will be exposed or sold to fellow criminals does not work if they cannot read any of your data and have no way of accessing the content. You may have been hacked and/or your system is being held hostage, but it is no more than, albeit slightly loaded, "an inconvenience" if your data is safe. There is no risk of data breaches or blackmail pressure, as there is no big deal to negotiate for these cyber criminals.
So, how do you secure your data? At least not with the usual encryption methods, because they will no longer hold up with the advent of quantum computers. With a quantum computer, encrypted files are decrypted in no time and then you nevertheless are screwed.
How to secure and why?
You better consider quantum-secure encryption because, as mentioned, quantum computers have the potential to break through traditional encryption methods. And that was precisely the solution to secure confidential data and communication, was it?
Quantum computers use a different computer architecture than classical computers, allowing them to factor large numbers exponentially faster than classical computers. Quantum computers can break through traditional encryption algorithms such as RSA or elliptic curve cryptography with the greatest ease.
That is why we offer our solution with encryption algorithms to address the potential threat of quantum computers. These algorithms are designed to be guaranteed to be secure against attacks from both classical and quantum computers and several combined techniques are used to encrypt data. For example, you can think of grid-based cryptography or hash-based cryptography.
By implementing quantum-safe encryption, you can ensure that your sensitive data is 100% protected, even if it comes into the hands of cybercriminals using a quantum computer.
The DBV Quantum-Safe Data Encryption provides a four-layer encryption, consisting of a combination of different encryption techniques.
Each encryption system is configured custom-made, so only you can decrypt your data with a self-created “passphrase”. No keys are stored; not on the workstation and not on the network.
It takes only a few milliseconds to generate a key. After that, it disappears and cannot be found by anyone. Files can only be unlocked with your own passphrase.
So what can you encrypt? Well, everything from texts and files to complete databases.
Interested to learn more?
It’s our pleasure to explain more about our quantum-safe solution. Please visit our website and leave us a message with your contact details or call us to schedule a video chat. And of course, this will be without any obligation.
Türkiye Contact https://siriuskriminal.com/iletisim/
Sirius Kriminal signed a dealership agreement with DFEND [Tech for Secure World] regarding the quantum-based encryption system.
Sirius Criminal signed dealership agreement with Systool Company, which provides world-class, robust and affordable solution services with a focus on guaranteed data security, high data quality recovery, migration to the Cloud and digital forensic solutions and software.
CYBER SECURITY (SUMMARY)
ADVANCE THREAT PROTECTION
- Botnet Protection
- Malware Analysis and Anti-Malware Saolutions
- Sandboxing and Emulation
- Application Whitelisting
- Network Forensic
- Automated Security Analytics
RISK GOVERNANCE AND COMPLIANCE
- ISO 27001 / HIPAA / PCI & SOC
- Firewall Compliance and Managemen
- Configuration Compliance
- Audit and Compliance Analysis
NETWORK SECURITY
- Firewall Management
- Network Access Control
- Secure Network Design
- Unified Thread Management
- Remote Access Solutions
- Intrusion Detection and Prevention System
- Pentest
INFRASTRUCTURE SECURITY
- DNS Security
- Mail Security
- Unified Communication
- Security Information and Event Management (SIEM)
- Zero Day Vulnerability Tracking
- Logs and False Positive Analysis
APPLICATION SECURITY
- Web Application Security
- OWASP Top 10 and SANS CWE Top 25
- Database Activity Monitoring
- Content Security
- Secure File Transfer
- Web Application Firewall
- Secure Coding Practices
- Testing for Vulnerability Validation
- Application Pentest
- Secure Code Review
SYSTEM SECURITY
- Windows / Linux Server Security
- Vulnerability / Patch Management
- Automated Vulnerability Scanning
DATA SECURITY
- Data Encryption
- Data Leakage Prevention
MOBILE SECURITY
- Authentication and Onboarding
- Rogue Access Point Detection
- Wireless Security Protocols
- OWASP Mobile Top 10
- Mobile App Automated Scanning
- Dynamic Mobile App Analysis
- Secure Coding Practices
- Mobile Pentest
- Secure Code Review
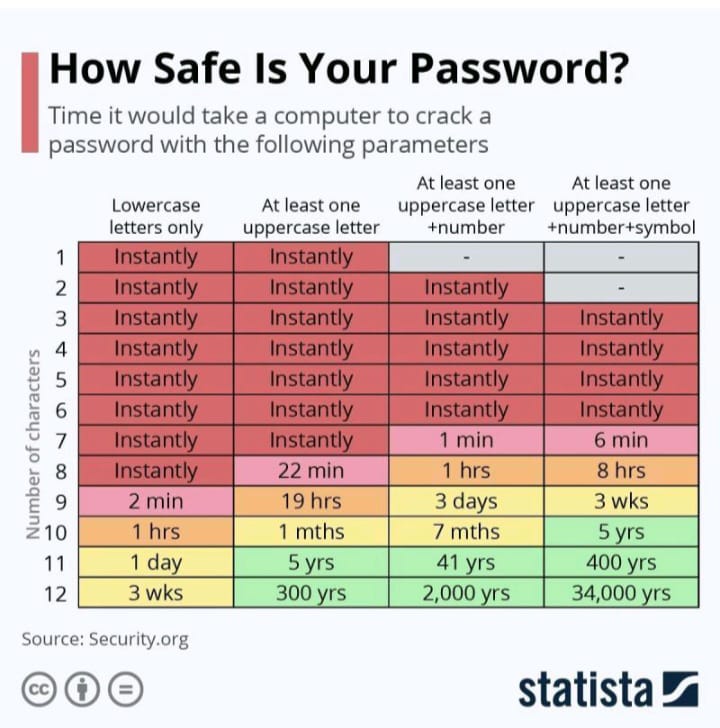
Password Cracking Times
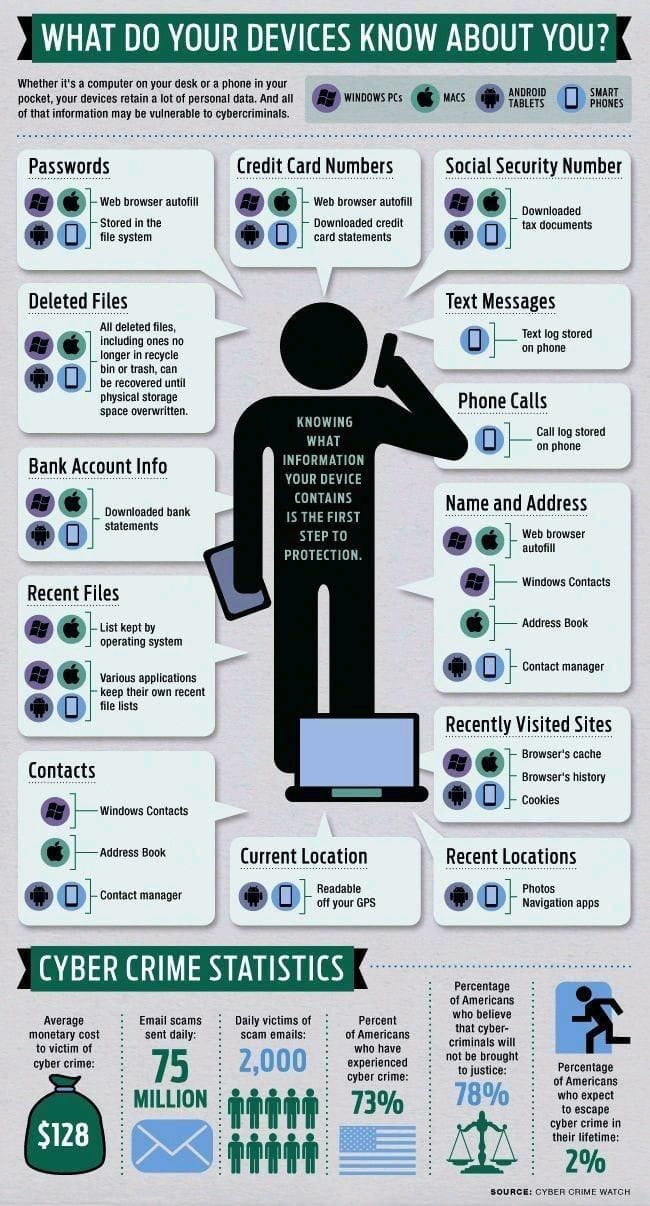
What do your devices know about you?
Disaster Victim Identification (DVI): Case Studies from the Afghanistan Aircraft Crash and Mass Graves in Kosovo Turkey–Kosovo Forensic Sciences Days



The second of the Kosovo Turkey Forensic Sciences Days, the first of which was held in Prizren-Kosovo in 2014 was held in Foça-İzmir on 25/26 April. We took part in the event with our presentation "Identification of Disaster Victims in Afghanistan Plane Crash and Kosovo Mass Graves".
Books on Law Enforcement
1- Practical Crime Scene Investigations for Hot Zones; J.T.Fish, R.N.Stout, E.W.Wallace; Practical aspects of criminal and forensic investigations series; CRC Press; Taylor&Francis Group
2- Emergency Response Handbook for Chemical and Biological Agents and Weapons; John R. Cashman; CRC Press; Taylor&Francis Group
3- Women Who Sexually Abuse Children; Hannah Ford; NSPCC
4- The Explanation of Crime; Context, mechanisms and development, Cambridge edited by Per Olaf W. Wikstrom and Robert J. Sampson
5- The Information Security Dictionary Defining the Terms that Define Security for E-Business, Internet, Information and Wireless Technology; Urs E. Gattiker; Kluwer Academic Publishers
6- Terrorism and Organised Hate Crimes; Intelligence gathering, analysis and investigatios; Michael R. Ronczkowski; CRC Press
7- Techniques of the Professional Pickpocket; Wayne B. Yeager
8- Sexual Murder; Catathymic and Compulsive Homicides, Louis B. Schlesinger; CRC Press
9- Serial Offenders, Current Thought, Recent Findings; Edited by Louis B. Schlesinger, Ph.D. ; CRC Press
10- The Human Skeleton in Forensic Medicine; Third Edition; Mehmet Yaşar İşçan, Maryna Steyn
11- Manual of Forensic Odontology; Edited by David R. Senn
12- Adli Bilimlerin Temeli; Mea M. Houck, Jay A. Siegel, Çeviri Editörü Yeşim Doğan
13- Advances in Forensic Human Identification; Edited by Xanthe Mallett, Teri Blythe, Rachel Berry
14- Adli Dil Bilimi; Editörler Prof. Dr. Selma Elyıldırım, Prof. Dr. İsmail Hamit Hancı, Seçkin Yaınları
15- Crime Scene Analysis and Reconsruction; Ross M. Gardner, Tom Bevel
16- Cadavar Dog Handbook; Forensic training and tactics for the recovery of human remains; Andrew Rebmann, Edward David, Marcella H. Song
17- Crime Scene Reconstruction; W. Jerry Chisum, Brent E. Turvey
Forensic DNA Phenotyping (FDP)
By comparing samples, DNA collected at a crime scene can be matched to a suspect, or it can be used to determine a suspect’s physical appearance. A forensic scientist can sequence a DNA sample and provide investigative authorities with information about distinguishing characteristics such as the suspect’s hair, eye and skin color, age, and biological ancestry.
Immunochromatography
Immunochromatography tests are used in forensics to detect drugs and pharmeceuticals in a subject’s bodily fluids. A smartphone-based sensor has even been developed to perform immunochromatography on a saliva without the requirement for a lab visit.
Forensic Geolocation Using Stable Isotope Analysis of Water
Scientist can pinpoint where a sample came from by isolating the isotopes in a water sample found on a suspect or victim, according to recent findings. If there are enough samples, the isotopes can even reconstruct the subject’s route. Other methods of isotopes detection can be used to ascertain the number of persons present.
Automotive Digital Forensics
Digital vehicle forensics refers to the identification and analysis of digital data (digital evidence) extracted from vehicle systems and is known as digital vehicle forensic investigation. This information can provide valuable insights for legal and criminal investigators working on cases involving traffic accidents, theft, fraud, and other criminal activities in which vehicles are involved.
Digital Monitoring of Xbox Online Multiplayer Digital Distribution Systems Using the XFT Device
Most people do not think of a gaming system as possible spot to store illegal data, which is why criminals have become so reliant on them. The XFT is being created to give authorities visual Access to hidden files on the XBOX hard drive, making it one of the most groundbreaking forensic Technologies for digital forensic specialist